Editor’s note: This is the first of a couple of Weelunk stories Earl Nicodemus is planning regarding cyber safety. The next one will be about cyber security for adults.
The chances of your child being harmed or killed by a stranger who they meet online are about the same as your odds of being killed by lightning. However, you know enough to avoid playing outside during a thunderstorm. By far, most of the American children who are abducted and harmed are abducted and harmed by someone they know. However, stranger abductions are becoming more common in America.
One thing that you can do is to make sure that your children and grandchildren are safe when they are online. The purpose of this story is to help you to do so.
Before you read the scenario below, I will tell you that it is based on information about a real girl who gave me permission to use her as an example. I have changed the names and the locations in the story to protect her identity, and she has since deleted the MySpace profile and made her Facebook page more private. I wanted to find out if I could figure out who she was from a very small amount of information provided in an online chat. Please note that the chat was simulated.
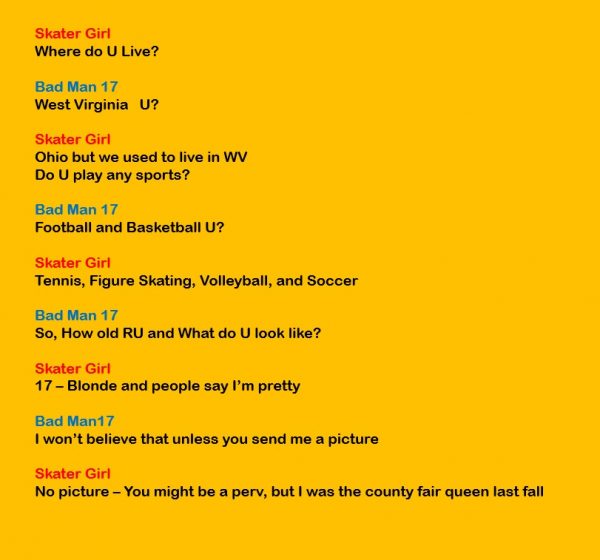
What do we know about Skater Girl from this online chat?
She is a girl.
She is 17 years old.
She does Tennis, Figure Skating, Volleyball and Soccer.
She used to live in West Virginia, but currently lives in Ohio.
She is blonde.
Her user name is Skater Girl.
When I did this demonstration in my Instructional Technology classes, I used the real information from the girl who gave me permission to do so. The names in this screen capture and the one below have been changed to protect that young lady. I started by Googling the user name of “Skater Girl.”
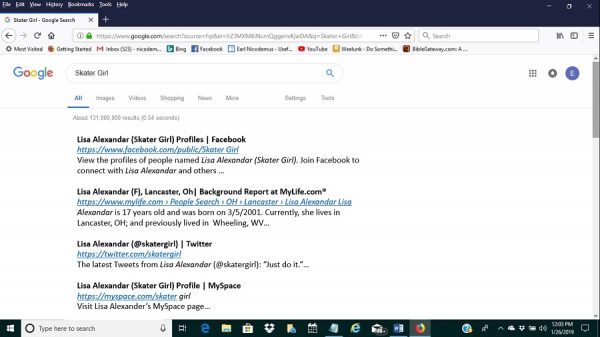
The most promising hit for Skater Girl was Lisa Alexandar, so I did a Google search on that name. Here is what came up.
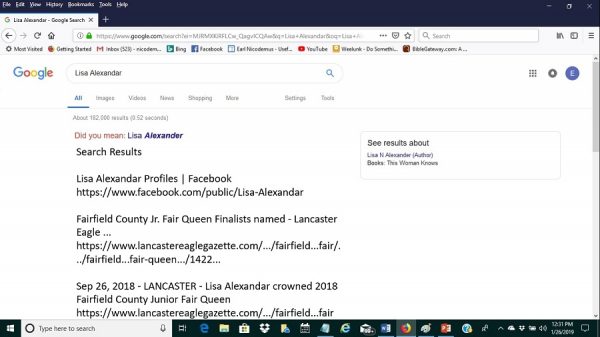
My real subject also had an unusual user name and last name. Note the spelling of Alexandar instead of Alexander. On our real demonstration, an obituary in the Wheeling paper came up. It was for the girl’s grandmother, and it listed the names of her parents and siblings and mentioned that they resided in Ohio: “Formerly of Wheeling, WV, now living in Lancaster, Ohio.” Also, the news story about the county fair queen for our real girl gave the names of her parents and told where they lived and where she attended school along with a list of her school activities.
In addition, her MySpace page was not secure. It reinforced that Skater Girl was Lisa Alexandar and included lots of pictures of her including sports team pictures that gave her school and a whole bunch of county fair queen pictures. It even said that she used to live in West Virginia. It also included the names of her mom, dad and siblings. By doing a google search on her dad’s name, we were quickly able to obtain a street address for the family that we put into the search box on Google Earth. Google Earth gave us a street-level view of their home that was clear enough to read the number on the mailbox and showed the family vehicles in the driveway.
At this point, in every class, someone (almost always a young lady), would raise a hand and ask if this demonstration was real. In response, I would show the class a screen capture of the FB Messenger exchange in which the subject gave me permission to creep her in front of a class and would assure the class that my young friend had taken care of the issues that made her so easy to find. (My students told me that a “creeper” was a pervert who “creeps” or cyberstalks people.)
Here is the bottom line. Even an innocent chat can provide more information than you or your child or grandchild realizes. To keep kids safe, keep them out of online chats. Before you assure me that you already do so, let me assure you that it is likely that they are chatting online without your knowledge. If they are playing online games on a cell phone, tablet or laptop, they are almost certainly chatting with other participants from within those games. I recently spoke to a sixth-grade boy who was telling me about the online game that he liked to play. I asked him if he ever chatted with the other players and he said, “All the time.”
Here are some specific suggestions for parents.
Make sure your children stay out of chat rooms and do not use the chat functions in online games or games on their phones and other devices. This will be difficult because other gamers will try to engage them in the chats.
Make sure that you know all of the child’s passwords and that you check his or her devices frequently to see what he or she is sending and receiving.
Sooner or later, your son or daughter is going to set up a Facebook page even if you forbid it. One mom told me that she had discovered that her 14–year-old daughter had created a Facebook page. She said, “I put an end to that real quick.” Several years later, I had that girl as a student at West Liberty. She told me that she had simply created another Facebook page using a different user name so her mom couldn’t find it and then updated it when she was away from home. Even if mom deleted the Facebook app, the teenager could simply log on using the web browser on her own device or on a friend’s device. Instead of trying to forbid those social media accounts, make sure you are a friend or follower on them.
Make sure that your child does not use his or her full name online. If the girl in our example had used her first and middle name instead of first and last name on her social media, it would have been much harder to find her using the info from the chat. If your daughter’s name is Mary Jane Smith, have her use Mary Jane without the last name. Even better, have her use some nickname which her friends and family members would recognize but which would be meaningless to anyone else. However, you need always to remember that you and your children are not anonymous when you are online.
Every time we go online, our Internet Service Provider gives us an IP address that is unique to us at that time. Anyone with whom we communicate online can easily capture that IP address and use free online resources to find out the region where that IP address is located. I looked up my IP address a few minutes ago and the site said that my IP address was located near Triadelphia, W.Va. I live in West Liberty. Before you tell me that the website got it wrong, remember that it was locating me on Planet Earth and that it came within 10 miles of my exact location! If I am a creeper and am interested in your son or daughter, that much information would help me to narrow down his or her identity and location.
Do not allow your child to use your credit card to purchase online games or to make purchases from within those games. If you want to purchase an app or game for them, make sure that the app or game does not store the credit card information thereby permitting easy one-click purchases from within the game. Some parents have been surprised with credit card bills in the thousands of dollars because of this mistake.
Cyberbullying is another big problem for young people who are online. Suicide is one of the leading causes of death for people aged 13 to 35 along with accidents, drugs and homicides. You can help by monitoring what is said to your child when he or she is online and what your child says to others online. Be sure to look at their chat and messaging logs and at what is being posted on their social media pages.
Advise your children to never click on links in emails or text messages. If they see a pop-up advising them to install an update or to approve a virus scan while surfing the net, they need to use the power button to force a hard shutdown and then get you or another adult to reboot and make sure the message is not a malware attack.
You might want to install an app that will filter what your child can access or do online. You can read PC Magazine reviews of some of the parental monitoring software at this site.
If your child has a smartphone or tablet, you need to review their chat and text logs on that device also. I know that your preteen or teen will complain that you are invading his or her privacy, but you need to make clear to them that one of the conditions of having that phone is that you have full access and can look at what they have been sending and receiving. Install “Find My iPhone” if your child has an iPhone or Google’s “Find My Device” if they have another brand and make sure it is working so that you can recover their phone or tablet if it becomes lost or stolen. By the way, that software can also help to track your child if he or she becomes lost or stolen while carrying that device.
For a fun and educational game about online safety to play with your kids, be sure to visit the Federal Bureau of Investigation Safe Online Surfing website at this address.
Click here to read some suggestions from Wired Magazine.
This link provides some great tips from Comparitech, a cyber security company, about keeping kids safe online.

The Internet provides a resource like no other that has ever existed through all of human history. Our children need to learn to safely use that resource so that they can benefit from all that it has to offer. However, we need to be sure they are safe. We also need to remember that all of the threats and risks that face you in regard to your digital and online life also threaten them. In future Weelunk articles, I am going to offer some advice about how you can also protect yourself from some of those risks.

